
Load Balancer is covered in AZ-700 exam. Azure Load Balancer has a new SKU offering released called as Gateway Load Balancer which provides high availability and high performance for the Network Virtual Appliance workloads. Network Virtual Appliance usually called as NVAs, are 3rd party deployments which is used for securing the environment hosted in Azure. Since workloads are deployed in Azure, most of the companies will have requirements on monitoring, filtering, packet capturing, having intrusion detection on inbound, outbound traffic flowing in that environment. But there is a problem in having single Network Virtual Appliance to filter all the traffic will lead to single point of failure. So, it is always recommended to place the NVAs behind the Load Balancer in HA setup to provide high availability and resilience to the environment.
With this SKU – Gateway Load Balancer, one can seamlessly forward traffic from a Load Balancer of your Application to the Gateway Load Balancer where the NVAs are deployed.
Below is the flow of end-to-end traffic from Client to your Application deployed in a VM behind Load balancer via Gateway Load Balancer:
- Client initiates traffic to the Public IP of the Load Balancer
- Traffic reaches the Frontend IP of the Load Balancer which is chained to the Gateway Load Balancer.
- Traffic will be forwarded to the Gateway Load Balancer where the NVAs are added to Backend pool. Gateway Load Balancer then forwards the traffic to one of the NVA in the backend pool.
- NVA will filter the packets based on the policy that is pre-configured and forwards the packet to the destination application VM.
- Application VM receives the packet and respond back to the NVA which in turn sends it back to the Load Balancer.
Also Read: How To Become Azure Certified and Prepare for Azure Certification?
Components of Gateway Load Balancer:
- Frontend IP configuration
- Load-balancing rules
- Backend pool
- Tunnel interfaces
- Chain
Note: Gateway Load Balancer can only of type Internal Load Balancer with HA configuration.
Now, let me walk you through the creation of Gateway Load Balancer via Azure Portal.
- Navigate to Azure portal and search for Load Balancer. Click on create.
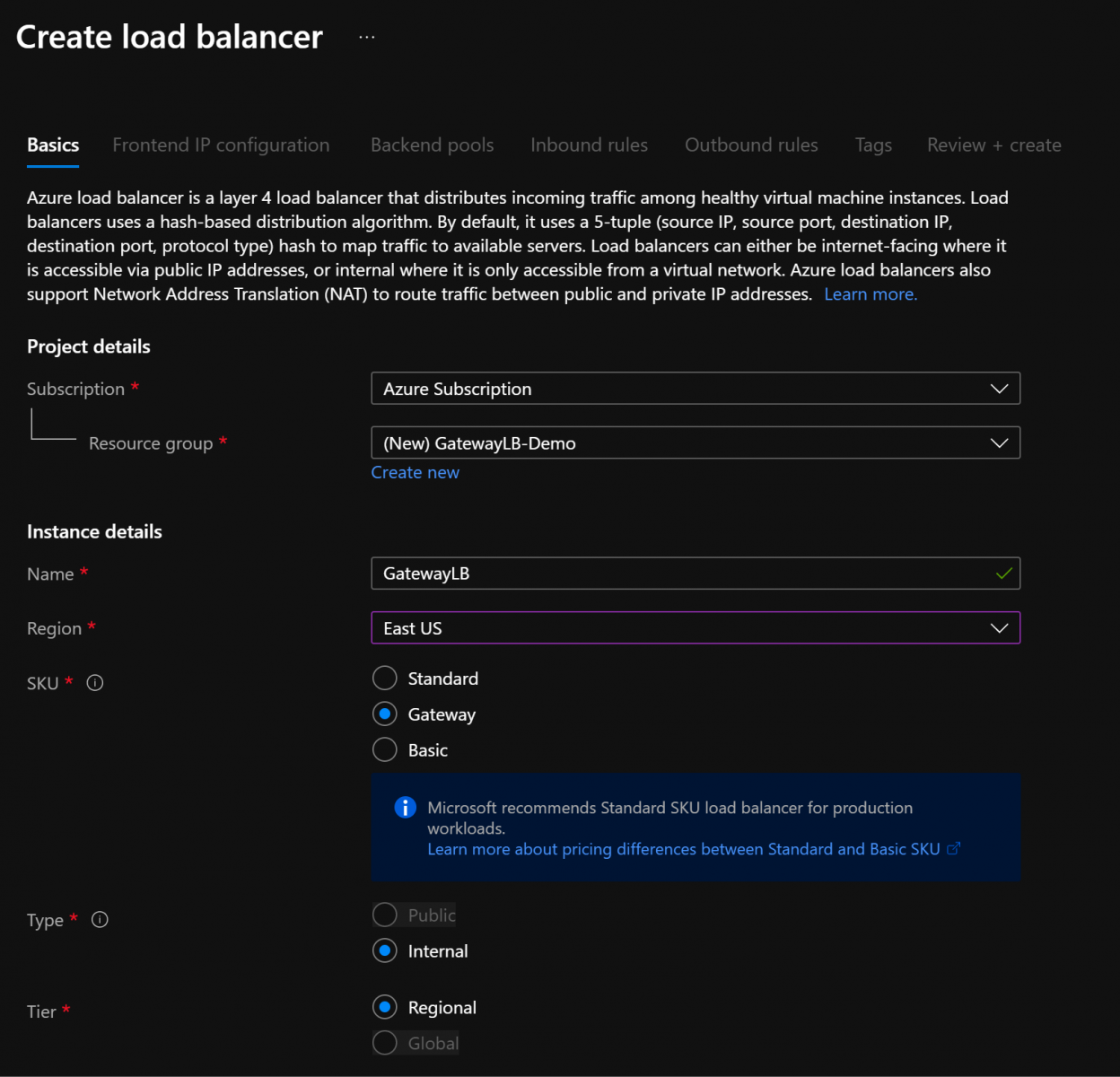
- Select your subscription where you want to deploy, Resource Group, Name, Region of your choice. In the SKU, select Gateway and in order to select the SKU as Gateway, type needs to be Internal, and tier needs to be Regional. Once, every entry is filled, click on Next.
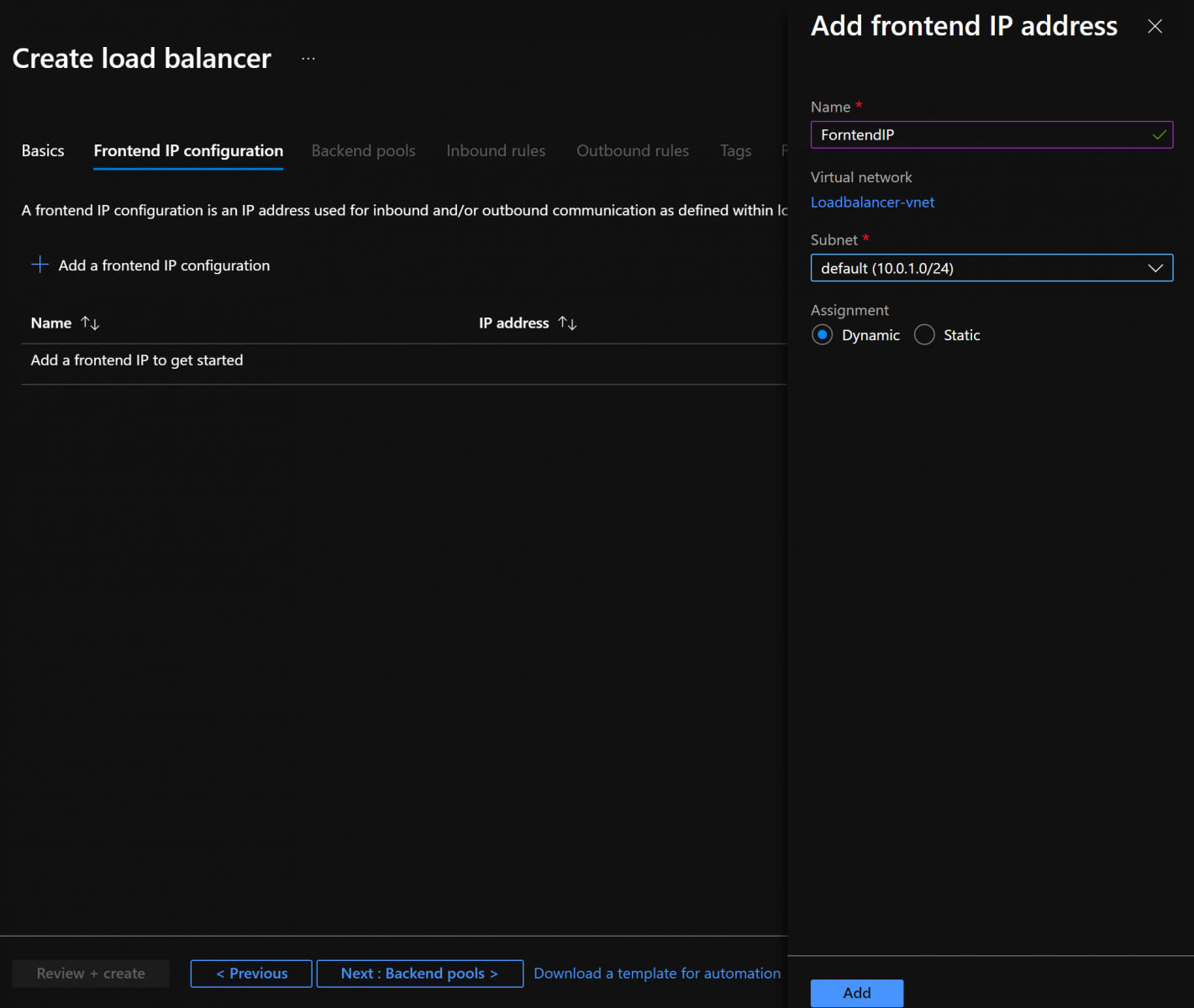
- In the Frontend IP configuration blade, click on Add Frontend IP address and type in the Name, select the VNET and subnet and click on Add. Once the Frontend IP config is added click on Next.
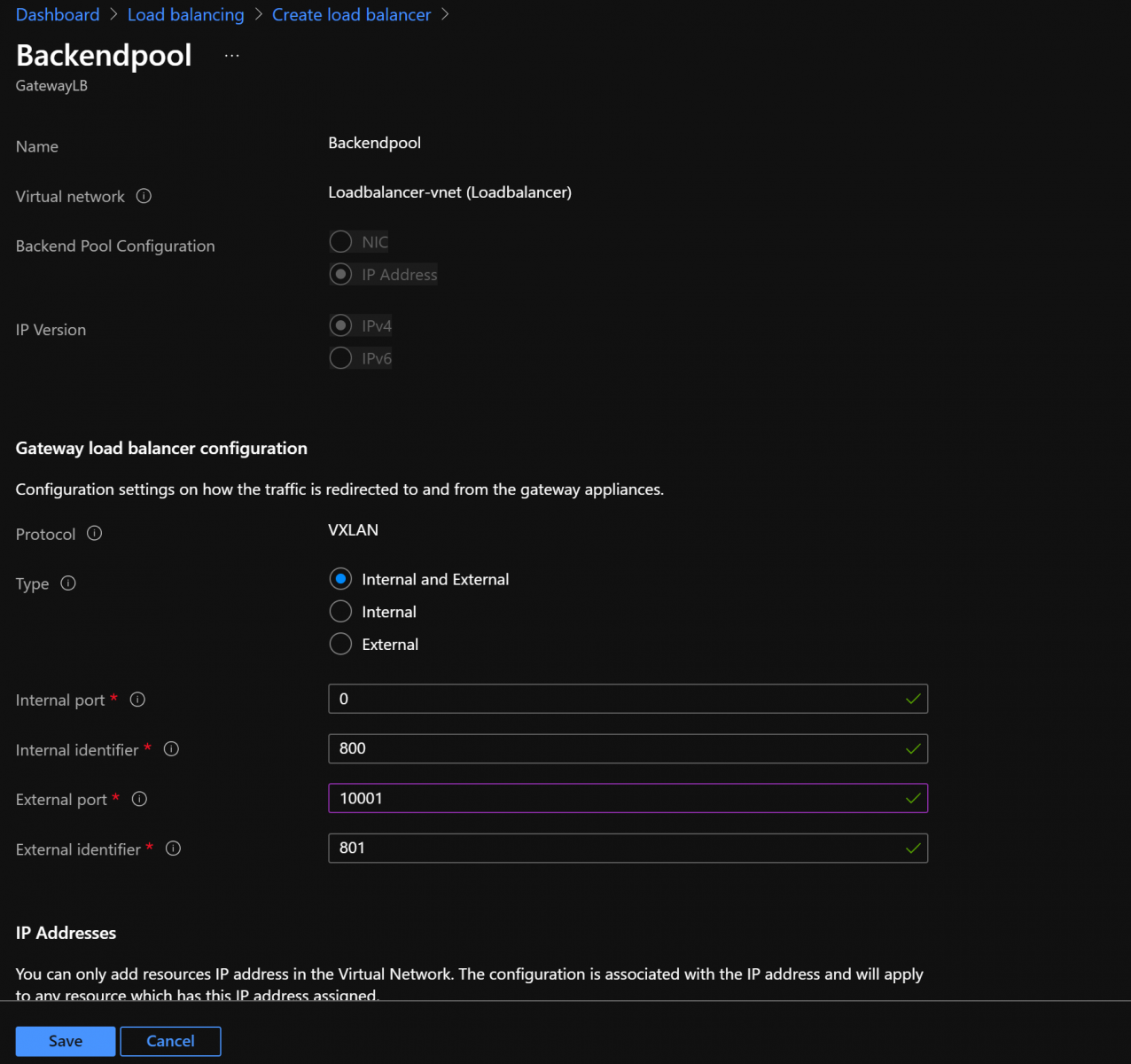
- In the Backend pool configuration, provide Name, VNET name, select the Backend Pool Configuration as NIC or IP Address and version. In the Gateway load balancer configuration select the Type as “Internal and External” and provide the corresponding Internal, External port and identifier. Add your NVA’s IP or NIC to the backend pool and click on Save.
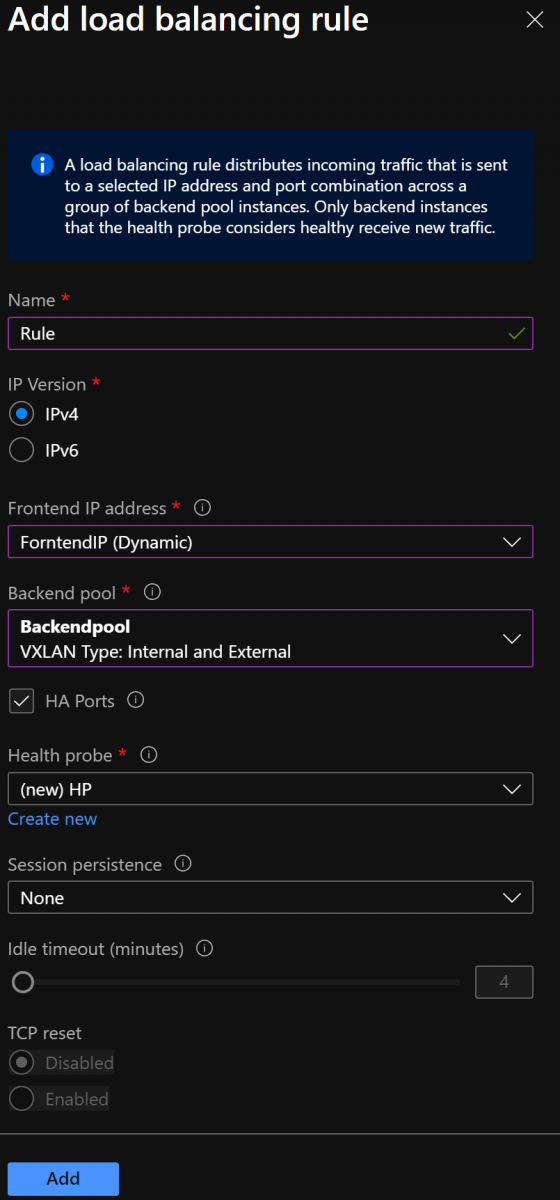
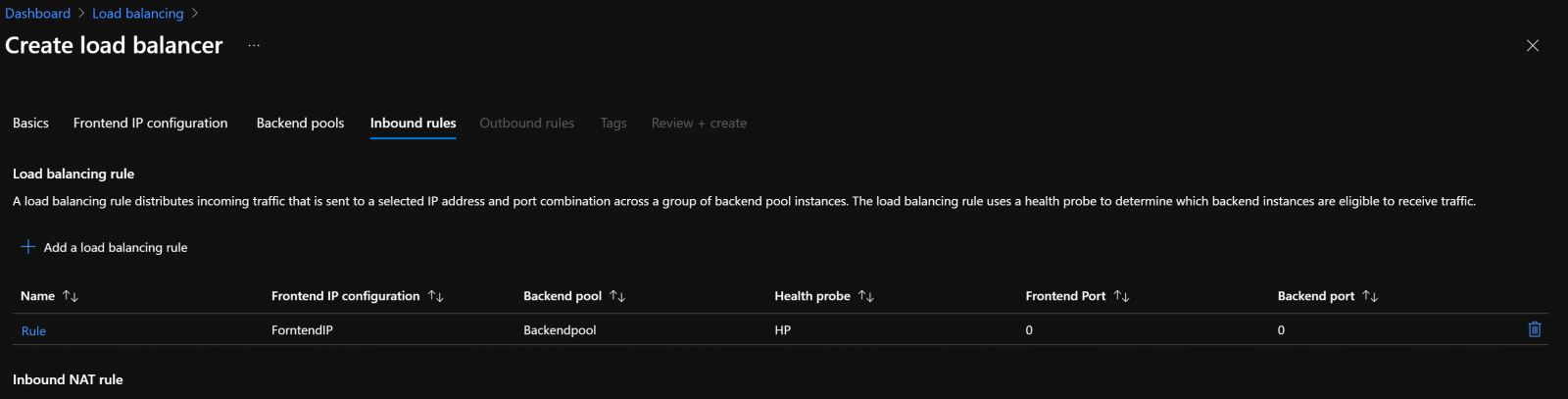
- In the Load Balancing Rule section, click on Add and provide Name, IP Version, Frontend IP address, Backend Pool, Health Probe, session persistence and click on Add.
- Click on Review and Create and once the validation is complete, click on Create.
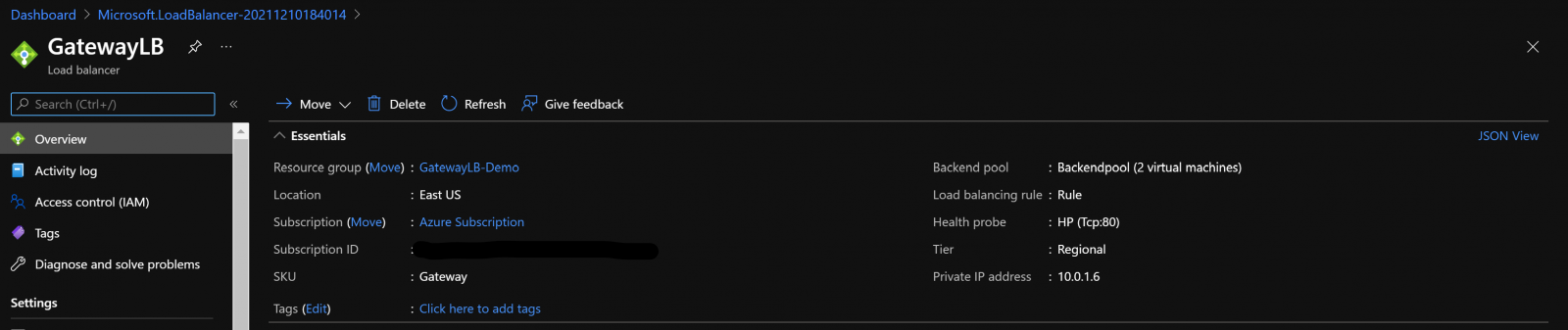
Once the deployment is complete, below is how the gateway Load balancer will look like in Azure Portal.
Current Limitation with Gateway Load Balancer:
- Gateway Load Balancer doesn’t work with the Global Load Balancer tier.
- Gateway Load Balancer portal support is currently unavailable in China cloud and Government cloud regions. CLI, PowerShell, Templates or alternatives can be used.
- Cross-tenant chaining is not supported through the Azure portal.
Also Read: What is the AZ-220 Microsoft Azure IoT Developer Certification?
Visit Microtek Learning – An authorized training provider for all Microsoft training and certification.
Or send a query so that our representative can call you back with the required information.

