In this blog, I am going to introduce a service called Azure Bastion and discuss more on the working, architecture, and why and when to use this product. This is an important product that is widely used to increase the security of the architecture that the customer has on the cloud. Moreover, this is a topic that you are preparing for AZ 305 and AZ 700 certifications.
When customers deploy their resources in Azure and want to access that resource there are many ways to do it. One such way is to access resources using the Internet using the resource’s public IP address. Another way is to use VPN (Virtual Private Network) or P2S (Point to Site) which is a secure way to access the resource. But the problem with VPN and P2S is that both need a Virtual Network Gateway which is chargeable per hour for the deployment and cost may increase based on the amount of traffic that is sent over the gateway. Another factor is that this setup will need configuration on the client side which adds up to the administrative cost.
Since accessing the resource over the Internet is a simpler and cheaper option security is a major concern. Let me explain how exposing a server’s SSH or RDP port to the Internet is risky. The number of attacks that are trending towards the servers on the cloud is increasing day by day and it is important not to expose your critical services’ RDP and SSH ports to the wide internet. So, the way architects design the system is by having a DMZ built which is exposed to the Internet and critical servers that are part of the network will not be exposed to the Internet. So, access to the servers will happen via the specialized server in the DMZ zone called Jump box.
Jump boxes are the servers that are typically VMs that are exposed to the internet. Now, the problem with the Jump box is that the server needs to be managed, and patched by the customers. In order to solve this problem Azure came up with a product called Azure Bastion which is a Microsoft-managed Jump box as a service.
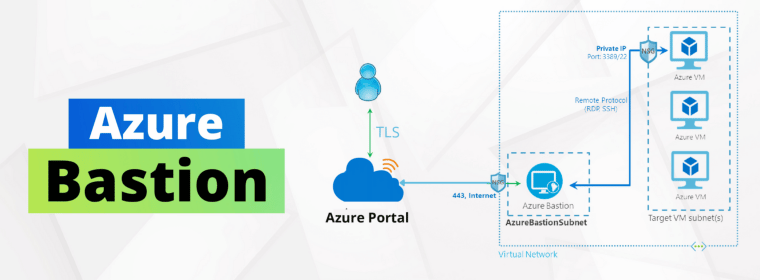
With this Bastion, one can access the Virtual Machine without using a Public IP address. RDP or SSH is possible via the browser which makes it easier for users who are using different Operating Systems. Since the entire session happens over TLS, it can bypass the firewall and users don’t want to contact their administrator to allow RDP or SSH access in their On-Premises. Since the Virtual Machine is not exposed to the Internet directly, the port scanning attacks can be prevented.
When a Virtual Machine is exposed to the Internet and in order to secure the server, the administrator will be using Network Security Groups to harden the server. This is a time-consuming process and there are changes of human error leading to exposing the server to the internet. With Azure Bastion, we can have a centralized place where the user can implement the Network Security requirements and it makes management easy. Bastion will be able to withstand any such attack.
What Benefits Does Azure Bastion Offer?
Users benefit from a managed jump server with Azure Bastion, which serves as a single point of access to their resources. Contrary to alternative methods, customers don’t need to handle intricate VPN configurations or use a jump-server VM’s public IP address, which is visible to the internet. Here are some more advantages of using Azure Bastion.
- Within the Azure Portal, users can RDP and SSH directly.
- Secure access to remote sessions is possible via HTML5 (HTTPS/443).
- It is not necessary to have a public IP address that is directly connected to the internet to use Azure VMs.
- Network security groups will not need to be managed by organizations employing the solution (NSG).
- There is no need for a firewall traversal when using RDP/SSH.
When Should You Use Azure Bastion?
For improving the security of virtual machines running on Azure, use Azure Bastion. Let’s examine a few of Azure Bastion’s application scenarios.
- Azure Bastion may be a solution if you are utilizing Azure VMs with a subscription that prevents you from setting up a VPN connection or a jump-host in an Azure vNet.
- Setting up Azure Bastion can be less expensive than using a jump-host or Azure terminal server if you have numerous administrators or users operating on the same host.
- For businesses that need to give users access to standalone VMs but do not need to grant them permission to use additional virtual network resources, Azure Bastion may be a solution.
- When you need to quickly install a bastion host for a brief period of time, it is the perfect solution for implementing just-in-time (JIT) Azure management without deploying permanent VMs.
How Do I Install Azure Bastion?
The Azure Portal allows for the deployment of Azure Bastion. Both PowerShell and already-existing Azure VM settings can be used to construct the bastion host.
Follow the procedures described below to add a new Azure Bastion host through the Azure portal.
- Choose the Create a resource option from the menu or the home page of the Azure portal.
- Browse the Marketplace and look for Bastion when a new page appears.
- Select the Networking category result that lists Microsoft as the publisher by clicking on it.
- Make a bastion page, then add the resource configuration on the following page.
- launch the deployment after the validation is finished.
How Do I Connect to Azure Bastion?
The Azure portal’s connection pane, which is used to access your virtual machines, allows you to establish a connection to Azure Bastion.
- For the virtual machine you need to access via the Azure interface, click Connect.
- On the Connect screen, click Use Bastion after selecting Bastion from the selection.
- After selecting the options for Name, Public IP Address, Subnet, and Public IP Address Name verify the information.
- Enter your VM login information, then click Connect.
When a VM is routed through Azure Bastion, your browser will display an RDP connection to it.
Azure Bastion comes with 2 SKUs:
1. Basic
2. Standard
Basic SKU has the following features:
1. Connect to destined VMs in peered virtual networks
2. Access Linux Virtual Machine Private Keys in Azure Key Vault
3. Connect to Linux Virtual Machine using RDP
4. Connect to Windows Virtual Machine using SSH
Standard SKU has the following features:
1. Connect to destined VMs in peered virtual networks
2. Access Linux Virtual Machine Private Keys in Azure Key Vault
3. Connect to Linux Virtual Machine using SSH
4. Connect to Windows Virtual Machine using RDP
5. Host scaling – Increasing the number of host instances lets Azure Bastion manage more concurrent sessions. Decreasing the number of instances decreases the number of concurrent supported sessions. Azure Bastion supports up to 50 host instances.
6. Can assign a custom port to the RDP or SSH sessions.
7. Connect to Linux Virtual Machine using RDP
8. Connect to Windows Virtual Machine using SSH
9. File transfer from the local machine to Azure Virtual Machine.
Working:
Azure Bastion needs to be deployed in a VNET with a subnet named “Azure Bastion Subnet” which needs to have a minimum of /26 prefix. When a user wants to connect to the VM, on the VM’s overview page the user gets an option named connect. When connect is clicked, the user gets to choose whether the user wants to use bastion or Private IP or its Public IP address. When clicking on Bastion, the user will need to choose the protocol whether it’s RDP or SSH based on the Operating System of the Virtual Machine. Once that is chosen and the user name and password are filled, a new tab opens where the RDP/SSH session is formed to the VM which is selected.
The data flows from the browser to the Azure Bastion over HTML5 and then gets terminated at the Bastion. Based on the protocol that is been chosen, Bastion creates a new connection to the VM which is present in the VNET with the protocol specified. This is how a user can get into the VM using Azure bastion.
Another important thing to note is that:
Below are the roles which are required by the user to access Bastion:
• Reader role for VM, NIC which has Private IP.
• Reader role on the Azure Bastion resource.
• Reader Role on VNET.
Currently, Azure Bastion is used to connect to a Virtual Machine which can be Windows or Linux-based systems, Virtual Machine Scale Sets, or Azure Devtest Lab machines.
Microtek Learning Can Help with Azure Bastion Deployment
One of the outstanding features for safeguarding and making access to virtual machines simpler is Azure Bastion. It is a solid platform-native solution that does away with the requirement for discrete internet-facing servers and makes managing Azure resources simpler. You may deploy and manage your Azure resources with the aid of Microtek Learning, a Tier 1 Microsoft CSP. Contact our Azure certification training specialists for help with Azure services, plans, and deployments. They are accessible 24/7 by phone, chat, and email.

